Azure storage security focuses on five key areas
Management plane security
The action that has an impact on the storage account
directly is referred to as the management plane. Using Azure Active Directory,
we can manage who has access to the services that have an impact on the storage
account.
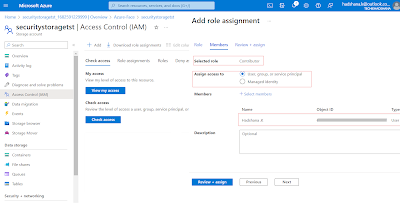
Role-based
access control
Every Azure subscription has an associated Azure Active
Directory, as we are all aware. Users, groups, and apps are all contained in
the Azure active directory. We can grant them access to the Azure
subscription's resources for management. This resource might be a storage
account, and we regulate the user's level of access to storage accounts by
giving them the proper role. Therefore, we can specify an owner role, contributor
role, or reader role.
Data Plane security
The techniques used to safeguard data objects (blobs,
queues, tables, and files) inside the storage account are referred to by this
phrase.
You can restrict who has access to the data in the storage
account in three different ways.
Azure active directory
access to queues and containers is authorized. Compared to
other methods of authorization, Azure Active Directory has benefits, such as
the elimination of the need for secret storage in your code.
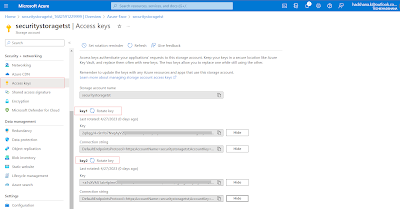
Storage account keys
Access to each information object in the storage account is
made possible by storage account keys.
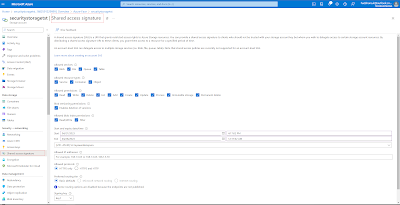
Shared Access Signatures
in the event that we want to restrict access to specific
services, such as blobs, queues, or a combination of both. Additionally, if we
want to restrict access to certain levels, such as read-only, update, and
delete, as well as if we want to offer access that is only valid for a certain
period of time. Due to security concerns, we only want to grant access for a
year at a time, and then we issue a new SAS and give it to them. We then employ
shared access signatures in that scenario.
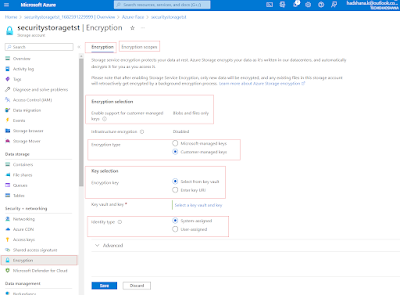
Encryption
in transit
HTTPS-based transport-level encryption
- When utilizing REST APIs or gaining access to a stored item, HTTPS should always be used.
- We can specify that only HTTPS should be used if SAS is being used.
Utilizing in-transit encryption for Azure file sharing
- Since 1 does not support encryption, connections are limited to those made within one region.
- 0 permits cross-region access and supports encryption.
encryption on the client side
- Before sending data to Azure storage, encrypt it.
- Data is received on the client side and then decrypted before being retrieved from Azure.
Resource
Sharing (CORS)
Cross-origin HTTP requests are those made by a web browser
for resources that are located on another domain.
CORS support is available through Azure Storage. We can
designate domains that have access to a certain storage account's resources for
each storage account.

Summary
In this article, we learned Azure storage security focuses
on five key areas. In our next article, we will learn Azure File Storage
Service.

0 Comments